Sebastian Österlund and Stephan van Schaik will give an in-depth talk on Intel’s new vulnerability at the second international conference on practical cybersecurity OFFZONE 2019.
Intel Product Security Center published several new side channel vulnerabilities called Microarchitectural Data Sampling. The RIDL speculative execution attacks allow threat actors to leak confidential data across arbitrary security boundaries on a victim system, for instance, compromising data held in the cloud or leaking your information to malicious websites.
“Speculative execution bugs in modern CPUs popped up out of nowhere, but the worst of the nightmare appears to be over. While Spectre-style attacks will be with us forever, a variety of mitigations have been implemented to protect us against Intel CPU vulnerabilities such as Meltdown and Foreshadow. Browser vendors have implemented process isolation, and Intel even have silicon fixes in their latest CPUs. Do you feel safe?” asked Stephan van Schaik.
“We destroy these mitigations by taking a skeptical look at their assumptions and reveal that unprivileged userspace applications can steal data by simply ignoring security boundaries. After all, what do address spaces and privilege levels mean to Intel’s CPU pipeline? Using our RIDL attacks, we’ll steal secrets from SGX using just a bit of JavaScript in a web browser, grab/etc./shadow from another VM without even thinking about the hypervisor in the middle and despair about our speculatively executed future,” commented Sebastian Österlund.
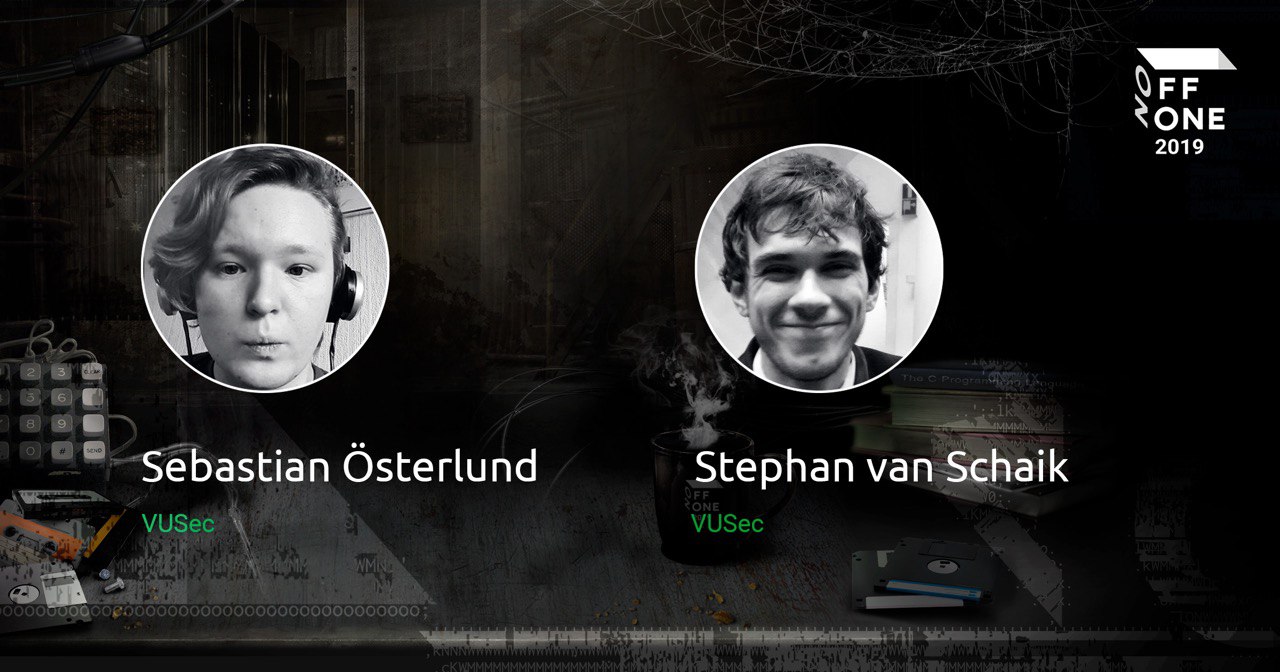
Sebastian Österlund is a PhD student in the Systems and Network Security Group at the Vrije Universiteit Amsterdam (VUSec) . His interests include memory safety, operating systems defenses, and fuzzing. Previously, he has worked on kMVX, a comprehensive kernel defense against information leaks using multi-variant execution, and more recently has worked on finding software bugs through directed fuzzing.
Stephan van Schaik is a PhD student in the VUSec group at the Vrije Universiteit Amsterdam. He is interested in the low-level side of computer science with a focus on computer micro-architectures, embedded hardware, and operating systems, but more specifically how these can be exploited within software-based attacks.